Control the Data. Protect the Calls. Trust the Platform.
A Secure Phone System Is Not Just Encrypted Audio.
Authentication Built for Real Operational Risk.
JWT Authentication with HttpOnly Cookies
Sessions use short-lived JWT access tokens stored in HttpOnly cookies rather than exposed browser storage, reducing common session theft vectors.
Refresh Token Rotation
Short session lifetimes and refresh rotation reduce the window of abuse if a token is ever compromised.
Password Policy Controls
Admins can enforce password length, complexity, lockout thresholds, and reuse prevention to match internal policy.
Two-Factor Authentication
Optional TOTP-based 2FA can be enforced for administrators and other high-value roles.
Admin Dashboard
Operators can review active sessions, revoke access, and investigate unusual sign-in patterns from the administrative layer.

Not Everyone Should See Everything.
Access-Control Principles:
- Master Admin controls platform-wide settings and cross-tenant operations
- Tenant Admin manages users, routing, numbers, inboxes, and AI controls within a single tenant scope
- Agents and supervisors operate inside the permissions needed for daily work
- Tenant boundaries are enforced at the application and data-access layers
- Recordings, transcripts, voicemail, SMS, and reporting stay scoped to the right environment
Every Channel Protected in Transit.
Transport Security Measures:
- SSL / TLS for dashboard and API traffic
- Encrypted SIP signaling and media where deployment policy requires it
- Strong SIP credentialing for registered devices and endpoints
- Secure webhook signing for outbound event delivery
- Role-aware API access controls for external integrations
- Configurable IP allowlisting for sensitive admin surfaces
Calls, dashboard sessions, and automation traffic should all be treated as sensitive operational data. Cloud Voice Manager is built accordingly.
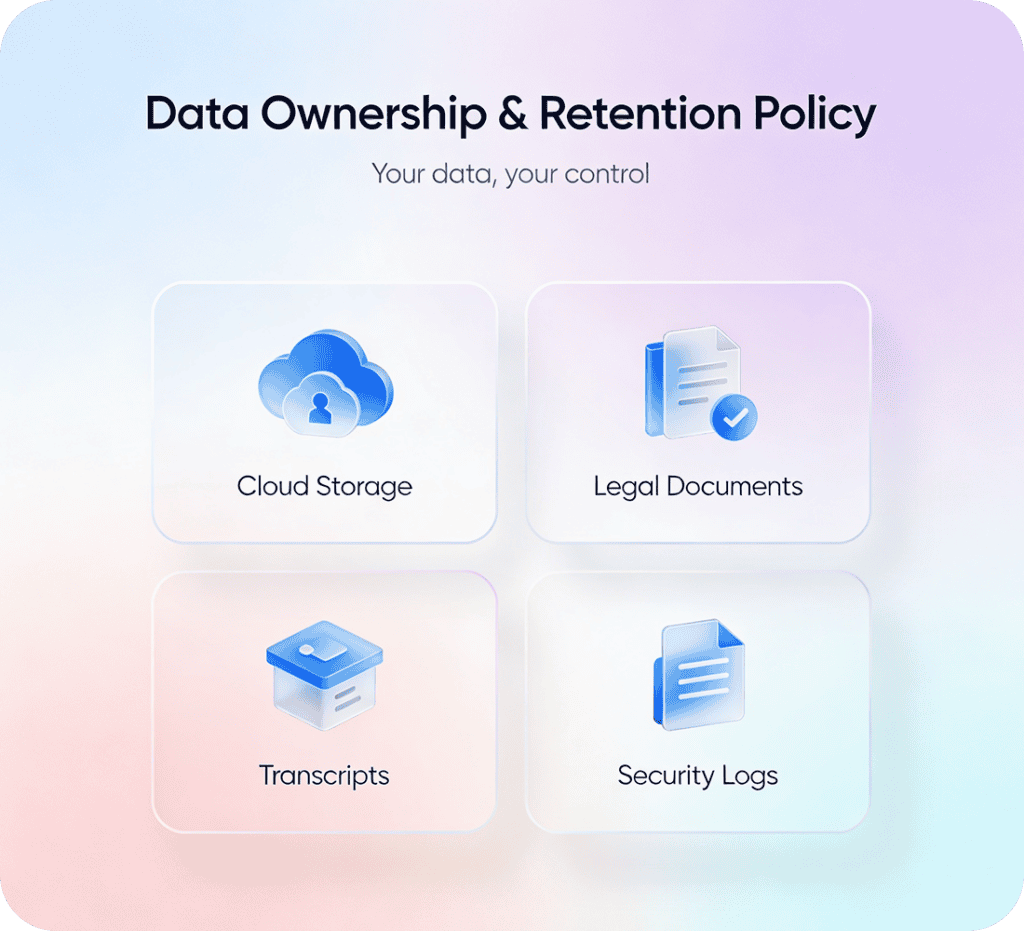
Your Retention Policy, Not a Vendor's Default.
What That Control Looks Like:
- Retention rules for recordings and transcripts
- Storage choices aligned to internal policy or infrastructure preference
- Legal hold and export workflows for sensitive recordings
- Searchability without surrendering storage ownership
- Clear linkage between call data and SALT CRM activity records
- Audit visibility into who changed settings and when
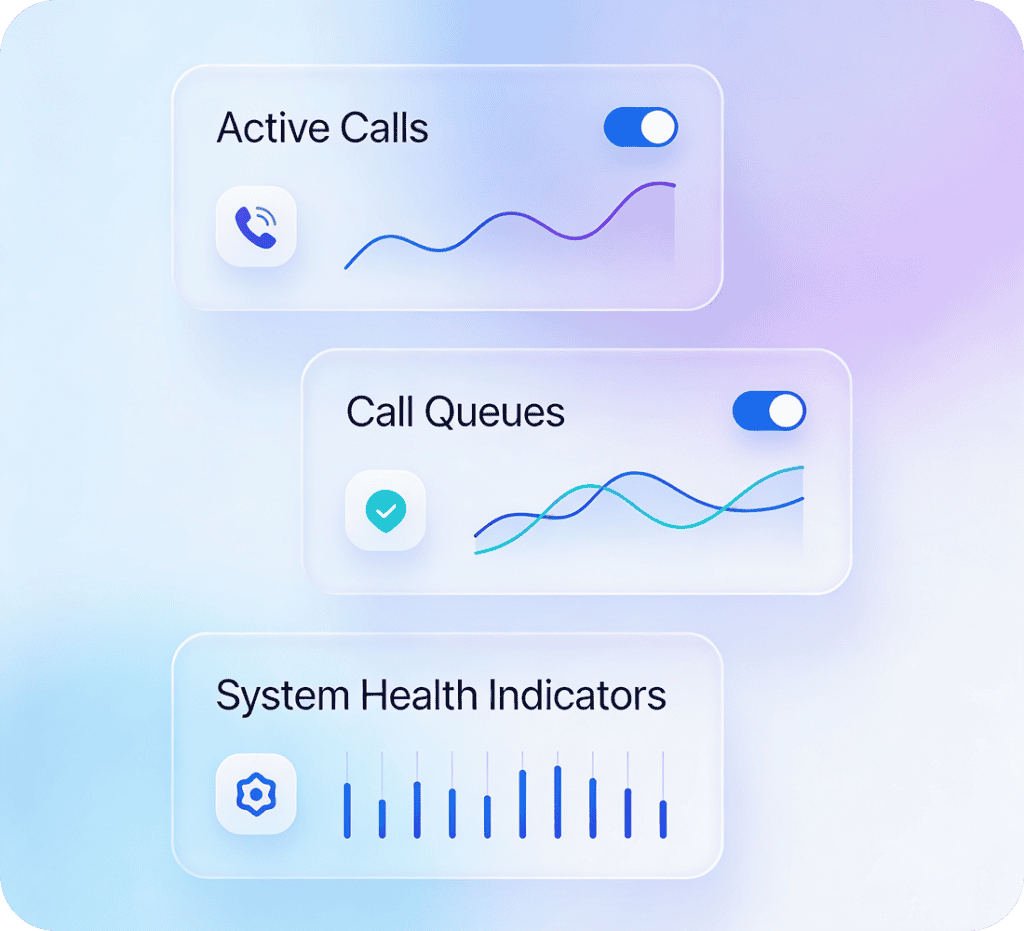
Reliability Is a Business Feature.
Customers do not care why a call failed. They care that it failed. Cloud Voice Manager is designed to reduce that risk with operational visibility and infrastructure-level discipline.
Reliability Principles:
- Carrier-grade telephony through Telnyx
- Real-time visibility into active calls, queues, and system state
- Audit logs for administrative actions and configuration changes
- Searchable call history for fast diagnosis
- Tenant-aware controls that reduce blast radius across environments
- Flexible deployment and storage strategy aligned to the operator's needs
Built to Support Policy, Review, and Accountability.
Cloud Voice Manager is designed to make policy enforcement and operational review easier.
Compliance-Supporting Capabilities:
- Audit trails for administrative actions
- Role-based permissions and tenant-scoped visibility
- Retention-policy control for stored communications data
- Searchable transcripts and recording access for investigation workflows
- Export paths for records that must move into internal review processes
- Self-hosted deployment that supports data-governance requirements

Why Buyers Trust the Platform.
Self-Hosted Control
Your data lives on infrastructure you control.
Scoped Access
Roles and tenant boundaries limit exposure by design.
Encrypted Traffic
Dashboard, API, and communications traffic are protected in transit.
Operational Accountability
Dashboard, API, and communications traffic are protected in transit.